Prompt Templates for Pro-level test cases
Get prompt-engineered templates that turn requirements into structured test cases, edge cases, and negatives fast every time.
Table Of Contents
- 1 Overview
- 2 What is Fuzz Testing?
- 3 What are the Benefits of Fuzz Testing?
- 4 Step-by-Step Instructions on How Fuzz Testing Works
- 5 When Should You Use Fuzz Testing?
- 6 Types of Fuzz Testing (With Use Cases)
- 7 What are the Limitations of Fuzz Testing?
- 8 Fuzz Testing vs Other Testing Techniques
- 9 Fuzz Testing in DevSecOps and CI/CD
- 10 5 Best Tools for Fuzz Testing that You Must Try
- 11 Final words: Start Fuzzing Where It Matters Most
- 12 FAQs
Overview
What is fuzz testing?
An automated testing method that bombards software with intentionally unexpected data to identify how systems fail under unpredictable conditions.
What are the benefits of fuzz testing?
- Uncovers memory corruption issues
- Exposes input validation gaps
- Catches edge-case logic flaws
- Supports compliance requirements
- Defends against modern attacks
When should you use fuzz testing?
- Launching new externally exposed APIs
- Processing complex file formats or protocols
- Handling security-sensitive operations
- Integrating third-party libraries or dependencies
- Deploying to high-risk environments
- Refactoring input validation logic
Imagine a user complaining that uploading a file crashes your application. Then another reports the same issue. Now your testing team is scrambling to figure out what happened.
Performance tests passed. Functional checks worked fine. API tests returned expected responses. You even tried random user scenarios manually. Yet production keeps breaking.
What could be the exact issue? Well, unexpected inputs your tests never considered, an empty field, or an oversized payload can crash services or expose vulnerabilities.
Fuzz testing stress-tests your system with intentionally messy inputs to catch these issues before users or attackers do. Let’s see how it works and how to add it to your workflow.
What is Fuzz Testing?
Fuzz testing is an automated testing technique that feeds random, malformed, or unexpected inputs into software to see what breaks. The goal is simple: find vulnerabilities and stability issues by deliberately sending data your application wasn’t designed to handle.
You don’t need to predict every possible failure. The fuzzer generates thousands of test cases automatically, showing bugs that sometimes don’t cross the mind.
Fuzzing works alongside your existing test suite to offer expanded coverage. While functional tests verify that features work as intended, fuzz tests verify that your application doesn’t fall apart when users enter invalid inputs.
For example, a fuzz test might send a login API thousands of requests with null values, special characters, or extremely long strings. If the API crashes or leaks error messages revealing the database structure, you’ve found a vulnerability that standard tests would miss.
What Are the Benefits of Fuzz Testing?
Fuzz testing isn’t just a technical safeguard. It protects business outcomes, compliance posture, and customer trust that directly impact revenue and reputation.
Here are the key benefits it delivers:
- Uncovers memory corruption issues: Finds buffer overflows, memory leaks, and use-after-free errors that lead to application crashes or allow attackers to execute malicious code.
- Exposes input validation gaps: Reveals where your code fails to sanitize user input properly, allowing SQL injection, XSS attacks, or data corruption through APIs and forms.
- Catches edge-case logic flaws: Shows race conditions, timeout failures, and unexpected state changes that only trigger when systems receive unusual input sequences
- Supports compliance requirements: Helps satisfy security frameworks like PCI DSS, HIPAA, and SOC 2 that require documented vulnerability testing.
- Defends against modern attacks: Protects your systems from techniques attackers actively use, including automated API fuzzing tools, protocol-level exploits, and weaponized file uploads.
Step-by-step Instructions on How Fuzz Testing Works
Fuzz testing systematically tests your application’s ability to handle bad data. Here’s how it works:
Step 1: Define Scope and Targets
Start by identifying components that process external input. Focus on areas where untrusted data enters your system:
- APIs: Endpoints that accept JSON, XML, or form data from users or external services
- File upload handlers: Components that process documents, images, videos, or any user-submitted files
- Parsers: Code that interprets configuration files, logs, or structured data formats
- Protocol handlers: Services managing network communication like HTTP, WebSocket, or custom protocols
- Microservices: Boundary services that accept requests from other systems or third-party integrations
You should also prioritize components at system boundaries and authentication layers where input validation failures have the highest impact.
Step 2: Choose Fuzzing Strategy
Once you’ve identified targets, decide which fuzzing approach fits your needs.
Mutation-based fuzzing takes valid inputs and randomly alters them by flipping bits, inserting characters, or truncating data. This works well when you have sample inputs but a limited understanding of the underlying format.
Generation-based fuzzing builds inputs from scratch using specifications or grammar rules. Choose this when testing structured protocols or file formats with strict requirements that mutation might not satisfy.
Step 3: Generate and Inject Inputs
After selecting your strategy, the fuzzer creates test inputs and delivers them to your target. Your web APIs receive malformed HTTP requests with corrupted headers or payloads. Moreover, command-line tools get invalid arguments, while file processors receive modified documents.
The fuzzer logs each input it generates. This tracking becomes essential later when you need to correlate specific inputs with the failures they caused.
Step 4: Monitor, Detect, and Log Failures
While fuzzing runs, track for signs of failure such as:
- Application crashes: Complete process termination or segmentation faults
- Hung processes: Operations that freeze or stop responding
- Timeouts: Requests that exceed expected response times
- Memory leaks: Gradual memory consumption increases that don’t immediately crash the system
- Assertion failures: Internal checks that trigger when code enters invalid states
- Unexpected error codes: Responses that shouldn’t occur under normal conditions
Once you figure out these failures, it’s important to log them. Make sure to capture the exact input that triggered the issue, complete with stack traces and system state at the moment of failure.
This data becomes your roadmap for reproduction and root-cause analysis in the next step.
Step 5: Analyze, Reproduce, and Fix
After fuzzing completes, review the failures it found. Start by reproducing each crash using the logged input to confirm it’s a real problem, not a monitoring glitch.
Once confirmed, dig into why that specific input caused failure. Identify whether it exposed missing validation, memory handling issues, or logic that couldn’t handle edge cases.
Patch the vulnerability or bug, then add the problematic input to your regression test suite. This ensures the same issue doesn’t resurface. Finally, integrate these tests into your CI/CD pipeline so every future build gets checked against these known failure patterns.
When Should You Use Fuzz Testing?
Fuzz testing isn’t necessary for every component or release. It is more beneficial when input validation failures cause the most damage or when traditional testing struggles to catch issues.
- Launching new externally exposed APIs: Endpoints accepting data from users, partners, or third-party systems need fuzzing to catch validation gaps.
- Processing complex file formats or protocols: Parsers handling PDFs, images, videos, or custom data structures contain intricate logic where edge cases hide bugs that functional tests miss.
- Handling security-sensitive operations: Authentication systems, payment processors, and access control logic require extra scrutiny to find vulnerabilities before they reach production.
- Integrating third-party libraries or dependencies: External code you didn’t write may handle unexpected inputs unsafely, so fuzz the integration points to verify behavior within your system.
- Deploying to high-risk environments: Production systems serving millions of users, regulated industries, or critical infrastructure need fuzzing as mandatory pre-deployment validation.
- Refactoring input validation logic: Any changes to sanitization, validation, or data processing bring regression risks that fuzzing catches before they cause incidents.
Types of Fuzz Testing (with Use Cases)
Fuzzing tests are of different types, each with its own strengths. Your choice depends on how much access you have to the code, what you’re testing, and what vulnerabilities matter most.
Here are the main types of fuzzing test:
| Fuzz Type | What it is | Visibility | Best for |
| Coverage-guided fuzzing | Uses code coverage feedback to guide input generation toward unexplored code paths | White-box or grey-box (requires source code or instrumentation) | Memory-safety bugs, crashers, tricky edge cases in parsers/libraries; maximizing path exploration |
| Behavioral/specification-based fuzzing | Generates inputs based on known specifications, protocols, or expected behavior patterns | Grey-box (requires understanding of expected behavior or specs) | APIs and services with documented contracts, where violations of expected behavior indicate security or stability issues |
| Black-box fuzzing | Sends random or mutated inputs without any knowledge of the internal code structure | Black-box (no source code or internal visibility needed) | Third-party libraries, closed-source systems, or legacy applications where you can’t modify or instrument the code |
| Protocol fuzzing | Targets network protocols by manipulating packet structure, headers, and message sequences | Can be black-box, grey-box, or white-box, depending on protocol knowledge | Network services, IoT devices, and applications using custom or standard protocols like HTTP, WebSocket, or MQTT |
| File format fuzzing | Mutates or generates files in specific formats to test how applications parse and process them | Typically grey-box (benefits from understanding file format structure) | Applications that process media files, documents, configuration files, or any structured file format |
What Are the Limitations of Fuzz Testing?
Fuzz testing excels at finding input-handling bugs, but it’s not a complete security or quality testing solution. It works best when paired with other testing methods that cover logic, business rules, and user workflows.
Here are some of its drawbacks that you should know about:
- Can’t verify business logic: Fuzzing finds crashes and memory issues, but won’t catch incorrect calculations, broken workflows, or features that work technically but produce wrong results.
- Misses authentication and authorization flaws: It rarely discovers privilege escalation or access control bugs that require valid credentials and specific user contexts to exploit.
- Generates noise and false positives: Not every crash or timeout represents a real vulnerability, requiring manual analysis to separate serious issues from edge cases that don’t matter.
- Requires significant computing resources: Running millions of test cases demands processing power and time, making it expensive to run continuously without proper infrastructure.
- Limited effectiveness on encrypted or compressed data: If inputs get encrypted or compressed before reaching vulnerable code, the fuzzer can’t generate meaningful test cases that survive transformation.
- Struggles with stateful applications: Applications requiring specific sequences of actions (login, then navigate, then submit) are harder to fuzz because random inputs rarely achieve the necessary state progression.
Fuzz Testing Vs Other Testing Techniques
Let’s take a look at how it is different from other test types:
| Technique | Objective | Input style | Automation level | Typical owners | When to use |
| Fuzz testing | Find crashes, memory issues, and input validation bugs | Random, malformed, edge-case inputs | High | AppSec, QA automation, devs | Testing APIs, parsers, and file handlers for unexpected input handling |
| Functional testing | Verify features work as designed | Valid user flows, business cases | Med – High | QA, devs, product | Confirming that business logic and user workflows function correctly |
| Fault-based testing | Simulate specific known failure modes | Targeted failure scenarios | Med – High | QA, devs, test architects | Testing error handling, failover mechanisms, and recovery processes |
| Robustness & destructive testing | Assess system behavior under extreme stress | Overloaded, boundary-exceeding inputs | Medium | SRE, QA perf, platform | Validating system limits and degradation patterns under load |
| SAST | Identify security flaws in source code | No runtime inputs (analyzes code) | High | AppSec, devs | Finding vulnerabilities like SQL injection or XSS during development |
| DAST | Detect runtime security vulnerabilities | Valid and malicious HTTP requests | Med – High | AppSec, security testers | Testing deployed applications for exploitable weaknesses |
Fuzz Testing in Devsecops and CI/CD
Fuzz testing offers the most value when it runs automatically as part of your development pipeline. Manual fuzzing catches some bugs, but continuous fuzzing integrated into CI/CD finds issues the moment they’re introduced, before they reach production.
Here’s how to integrate it into your CI/CD pipeline:
- Run lightweight fuzz tests during development: Execute quick 5-10 minute fuzzing sessions locally before you commit. This catches obvious input validation bugs early when fixes cost the least.
- Automate fuzzing on merge requests: Set up CI jobs to fuzz only the changed code, time-boxed to 15 to 30 minutes. It offers fast feedback and keeps your pipeline moving while still catching issues before they merge.
- Schedule nightly or weekly runs: Set up exhaustive fuzzing to run automatically during off-peak hours or weekends when resources are available. These longer sessions explore deeper code paths and identify complex edge cases that quick checks miss.
- Monitor production for fuzz-discovered patterns: Track whether issues found in fuzzing actually occur in real environments. This feedback loop helps refine which targets and strategies matter most.
Most CI platforms support custom test stages where fuzzing tools execute. Add fuzzing jobs to your configuration files just like you would unit or integration tests. If crashes are detected, fail the build and block deployment until fixed.
Metrics and Slas for Fuzz Testing
Track these metrics to measure fuzzing effectiveness:
- Code coverage from fuzz runs: The percentage of code paths exercised during fuzzing sessions, showing how thoroughly your input-handling logic has been tested.
- Unique crashes triaged: The number of distinct failures discovered and analyzed, separating real vulnerabilities from harmless edge cases.
- Time to fix fuzz-found bugs: The average duration between discovering an issue through fuzzing and deploying the fix to production.
- Crash reoccurrence rates: The percentage of previously fixed crashes that reappear in later builds, indicating whether fixes addressed root causes or just symptoms.
5 Best Tools for Fuzz Testing That You Must Try
The right fuzzing tool depends on your target system, available resources, and how much setup complexity you can handle. Here are five tools that are worth starting with.
1. Testsigma

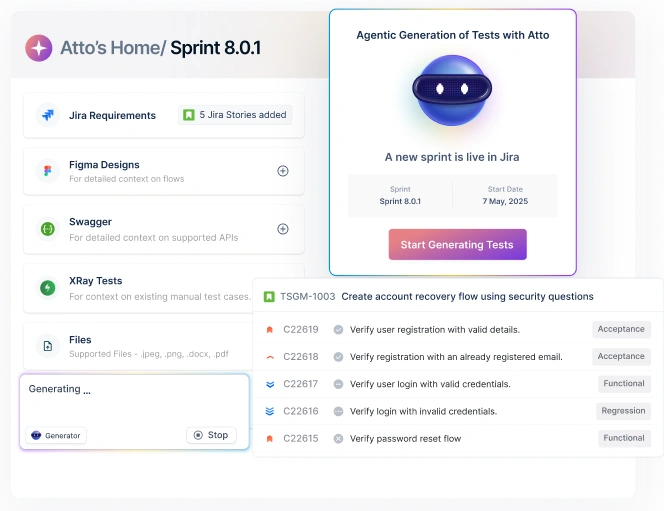
A no-code platform to write fuzz tests in plain English without scripts or code. You define test scenarios using natural language like “send random strings to login API.”
The platform generates randomized inputs, executes tests automatically in your CI/CD pipeline, and provides clear reports on what broke. Teams without dedicated security expertise can start fuzzing in hours, not weeks.
2. Afl (american Fuzzy Lop)
This coverage-guided fuzzer tracks which code paths execute during testing. It mutates inputs intelligently based on feedback, exploring new branches systematically. Moreover, it works well for C/C++ applications where you can compile with instrumentation.
3. Libfuzzer
An in-process fuzzer integrated into LLVM that runs fast and efficiently. You write small test harnesses calling specific functions with fuzzer-generated inputs. It’s best for testing individual libraries or components in isolation.
4. Peach Fuzzer
A commercial platform supporting file formats, network protocols, and APIs. It includes pre-built templates for common protocols and file types, reducing setup time for complex targets. Peach Fuzzer offers both mutation-based and generation-based strategies.
5. Burp Suite Intruder
Sends modified HTTP requests to APIs and web endpoints for manual security testing. It’s useful for exploring specific attack vectors, though less automated than dedicated fuzzers for continuous workflows.
Final Words: Start Fuzzing Where it Matters Most
Fuzz testing is a technique that works best alongside your other testing methods. It’s better suited for catching input validation bugs, memory issues, and edge cases that functional tests rarely surface.
Start fuzz testing small with one high-risk API or file handler. Run time-boxed tests in your CI/CD pipeline and expand coverage as you see value. Track code coverage, unique crashes, and fix times to measure progress.
Testsigma lets you add fuzzing to your test suite without leaving your automation platform. You can create scenarios that send randomized inputs to your APIs or forms, schedule them like any other test, and review failures in the same dashboard you already use.
No separate fuzzing infrastructure to maintain or specialized expertise required.
FAQs
Fuzz testing can be black-box, white-box, or grey-box, depending on whether you have access to source code and use coverage feedback.
No, fuzz testing also finds stability issues like crashes, memory leaks, and unexpected errors that affect reliability beyond security.
Run quick 15-30 minute fuzz tests on merge requests and comprehensive multi-hour or overnight runs weekly for deeper coverage.
No, fuzzing catches input-handling bugs but doesn’t verify business logic, user workflows, or functional correctness that other tests cover.